Page History
Versions Compared
Key
- This line was added.
- This line was removed.
- Formatting was changed.
| Equivalent |
|---|
Security is one of the most important considerations for Member.buzz. This outlines some of the security procedures in place to protect your information as you use our platform.
| Note |
|---|
This outline provides a technical insight into our platform beyond a user needs to use our platform. For a functional overview of how Member.buzz is secured, see Capabilities or our Security Splash Page. While this document provides some information on our compliance, our official legal terms is always the best source for our official policies. |
All vendors involved in our payment processing have fully-audited PCI Service Provider Level 1 certifications, which is the most stringent level of certification available in the payments industry. Member.buzz is also PCI certified separate from our vendors.
Data Security and Encryption
All traffic on Member.buzz is forcibly encrypted over HTTPS using a series of SSL certificates using the TLS 1.2 Protocol, a SHA 256 Signature, and an RSA 2048 Key.
All Member.buzz sites, including any Space without a custom domain, leverage certificates issues by the COMODO Certificate Authority. Spaces with a custom domain are automatically allocated SSL certificates using the Let's Encrypt Certificate Authority.
All data stored in our databases is encrypted at rest (using Transparent Data Encryption) and in transport (using SSL). Additionally, any Sensitive Personal Information (SPI) is encrypted before it reaches our databases, with one-way hashing used wherever possible. Whenever sensitive information is displayed in our user interface, it is either partially or fully masked.


Sensitive Data
As a payments-focused platform, Member.buzz may handle, transmit, or store sensitive information, including the following:
- Personal Information
- First and Last Name
- Phone Number
- Address
- IP Address
- Payment Information
- Bank Account Number
- Bank Account Routing Number
- Credit Card Number
- Credit Card Identifier (CCID/CVC)
All sensitive data is encrypted.
Infrastructure
Member.buzz is hosted in a series of three data centers, all located in the continental United States of America.
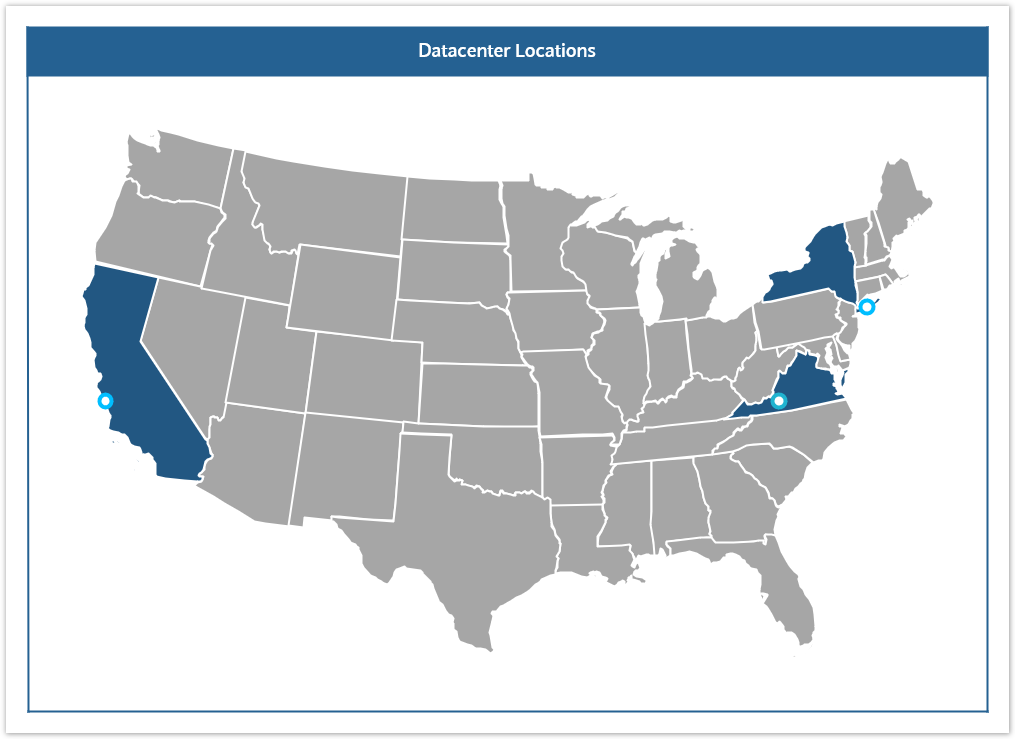
Each data center is actively monitored and protected with multiple layers of physical and network security. Firewalls are regularly patched, tested for vulnerabilities, and actively report any potential threats to our internal security team.
| Tip |
|---|
The Member.buzz platform is distributed between all of our data centers, making it impossible for individual spaces to choose where their data is stored. This gives us the ability to provide the fastest, most secure experience to all of our users. |
Access to our servers is highly restricted using centralized access controls and can only be initiated from within our physical internal network. All devices connected to our internal network are actively monitored, patched, and protected against malware.
All data is backed up to multiple sites and, in the event of a planned or unplanned outage, traffic is automatically routed to the remaining sites within a few seconds. In the event of an unplanned, catastrophic disaster affecting one of our data centers, our platform is designed to automatically failover within less than one hour.
| Nextsteps |
|---|
